Authenticate
Partner user signs into Drupal before reaching the protected extranet route.
Extranet proof of concept · Live on Hetzner
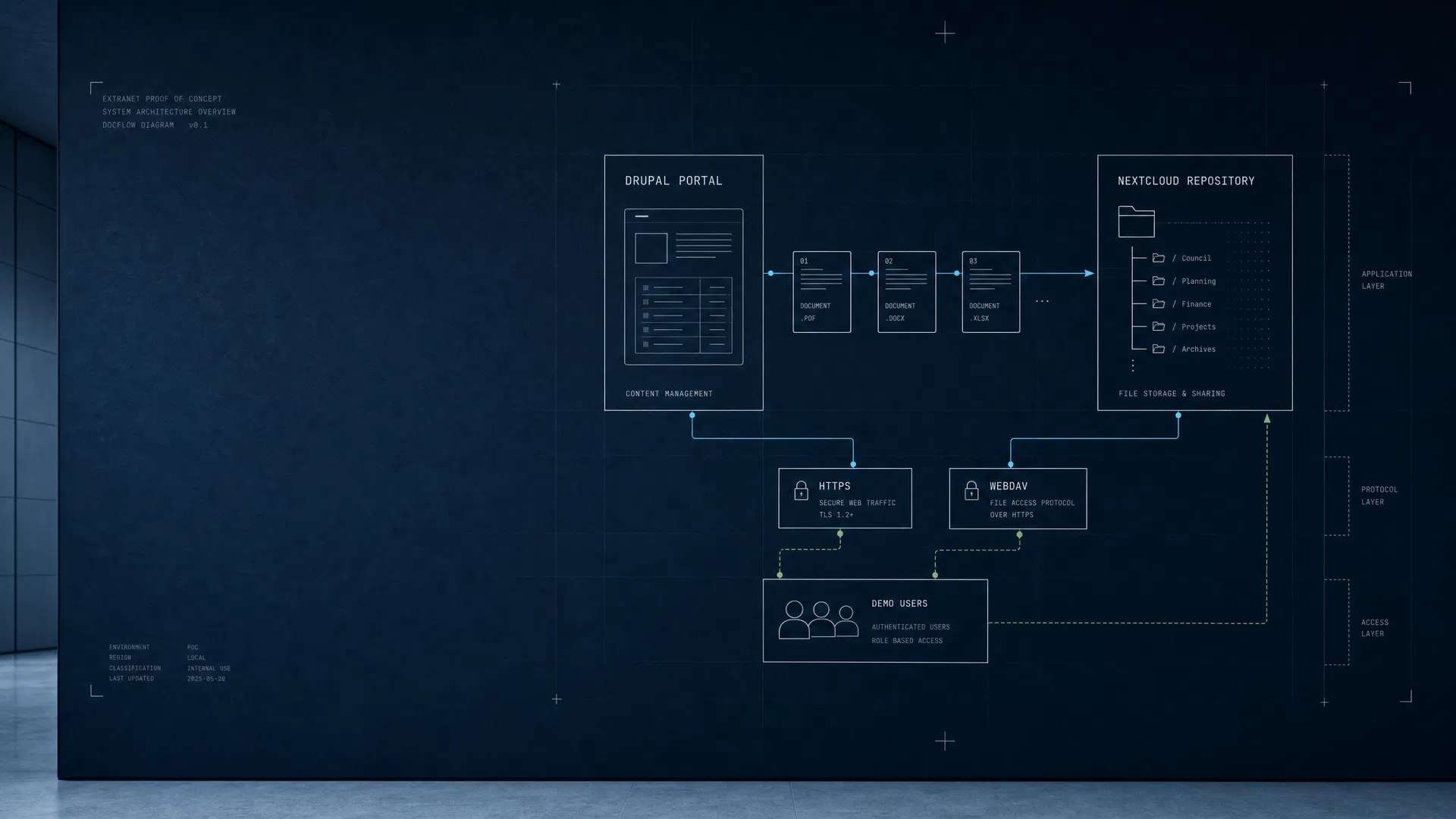
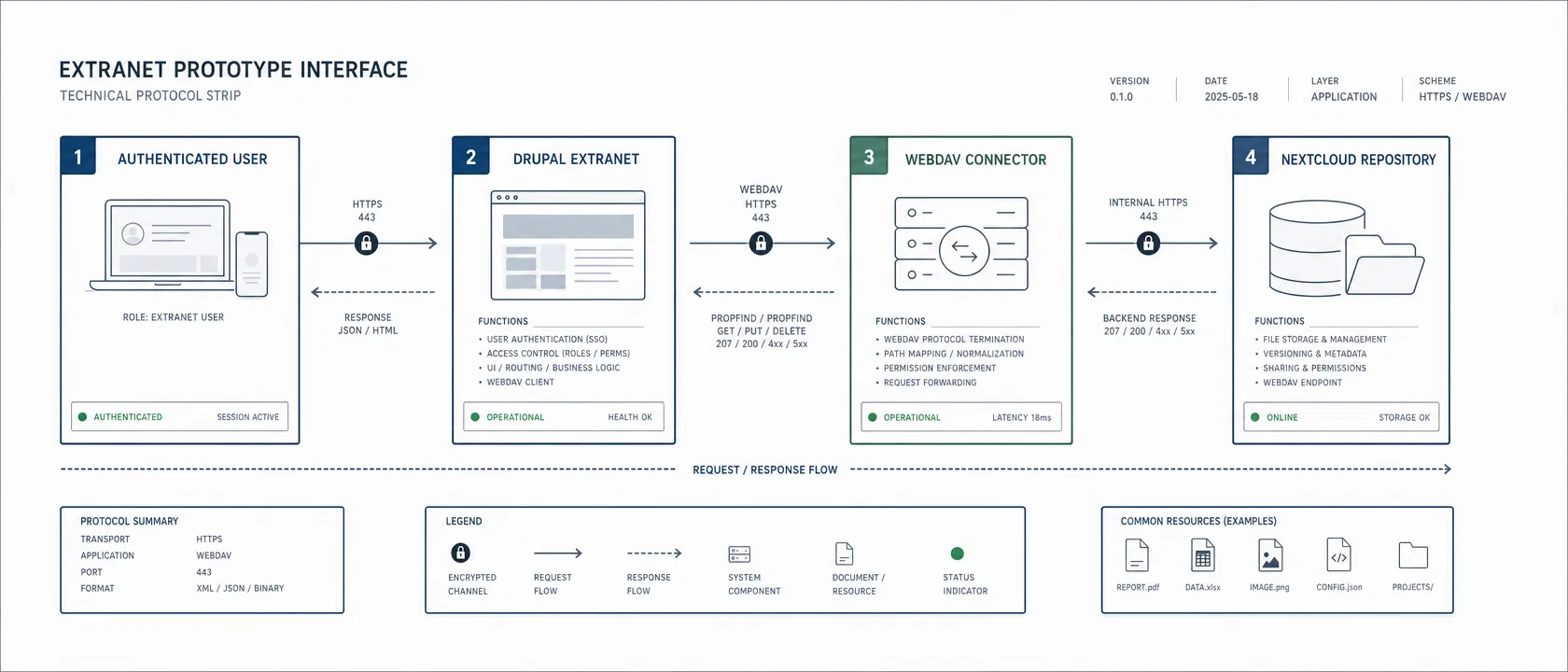
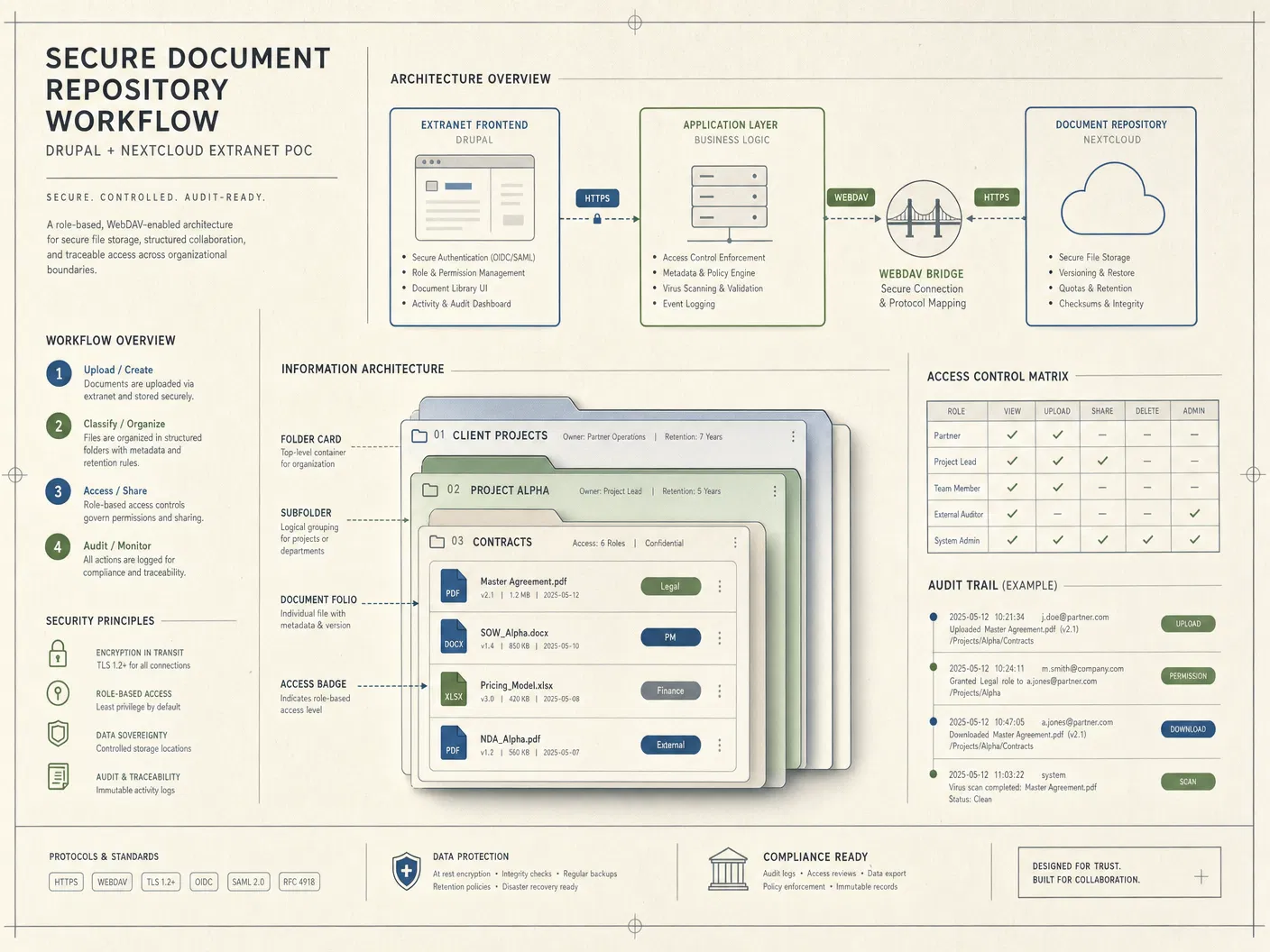
The POC is deployed behind HTTPS: Drupal acts as the authenticated partner portal, while Nextcloud stores repository files. The latest verification cleared a WebDAV 401 credential-drift issue and reconfirmed listing, uploading, Drupal-proxied document access, and direct Edit in Nextcloud actions.
Live endpoints
Demonstration workflow
The prototype is intentionally narrow. It proves that a Drupal extranet page can present repository state, push files into Nextcloud through WebDAV, provide Drupal-controlled downloads, and hand reviewers into the native Nextcloud file interface before the workflow is expanded into production-grade permissions, SSO, retention, and monitoring.
Partner user signs into Drupal before reaching the protected extranet route.
Drupal accepts a small demonstration document through the custom portal form.
The module sends the file to Nextcloud using the configured WebDAV account.
The dashboard lists the file, provides a Drupal download action, and opens the native Nextcloud file view for editing.
Build output
Drupal, Nextcloud, Caddy, MariaDB, and Redis are running on the Hetzner Docker host with public HTTPS routes.
portal.imextran.com · cloud.imextran.comCustom Extranet POC module with dashboard, settings form, permissions, WebDAV listing, browser upload, Drupal-proxied downloads, and Edit in Nextcloud actions.
extranet_pocPartner demo login, upload, listing, download, and Edit in Nextcloud actions were revalidated after the WebDAV 401 repair.
partner-demoCredential location, operational notes, validation evidence, and production hardening items are documented for the next refinement round.
POC_HANDOFF.mdValidation evidence
The portal was checked as both an anonymous visitor and an authenticated partner user. After a renewed WebDAV 401 caused by demo credential drift, the Nextcloud account was resynchronized with Drupal configuration, caches were rebuilt, and the upload path was retested through both direct WebDAV calls and the Drupal portal form. The dashboard was then extended and verified to render per-file Edit in Nextcloud buttons.
| Public HTTPS | Both hostnames resolve through Cloudflare and route to the Caddy reverse proxy. |
|---|---|
| Anonymous access control | The protected Drupal extranet route denies unauthenticated visitors. |
| Partner login | The generated partner demo account can sign in and see the Extranet portal menu item. |
| WebDAV listing | A direct Drupal-container PROPFIND to the Nextcloud `Shared` folder returned HTTP 207 after credential realignment. |
| WebDAV upload | A direct Drupal-container PUT returned HTTP 201 and readback returned HTTP 200 for `manus-webdav-smoke-20260505-223640.txt`. |
| Portal upload | Authenticated `partner-demo` upload automation detected the Drupal success state and no WebDAV failure message. |
| Edit in Nextcloud | The dashboard render test produced 5 `Edit in Nextcloud` buttons and a sample public Nextcloud Files URL without exposing WebDAV credentials. |
/opt/imotivat-extranet-poc/scripts/sync-demo-webdav-credentials.sh.